Basics
- Field Restrictions (or Field-Level Security) make it possible for specific data values on a record to be hidden from users via Security Roles. This means that a user with a Security Role prohibiting them from seeing a specific field on the Contacts page may not even know that field exists.
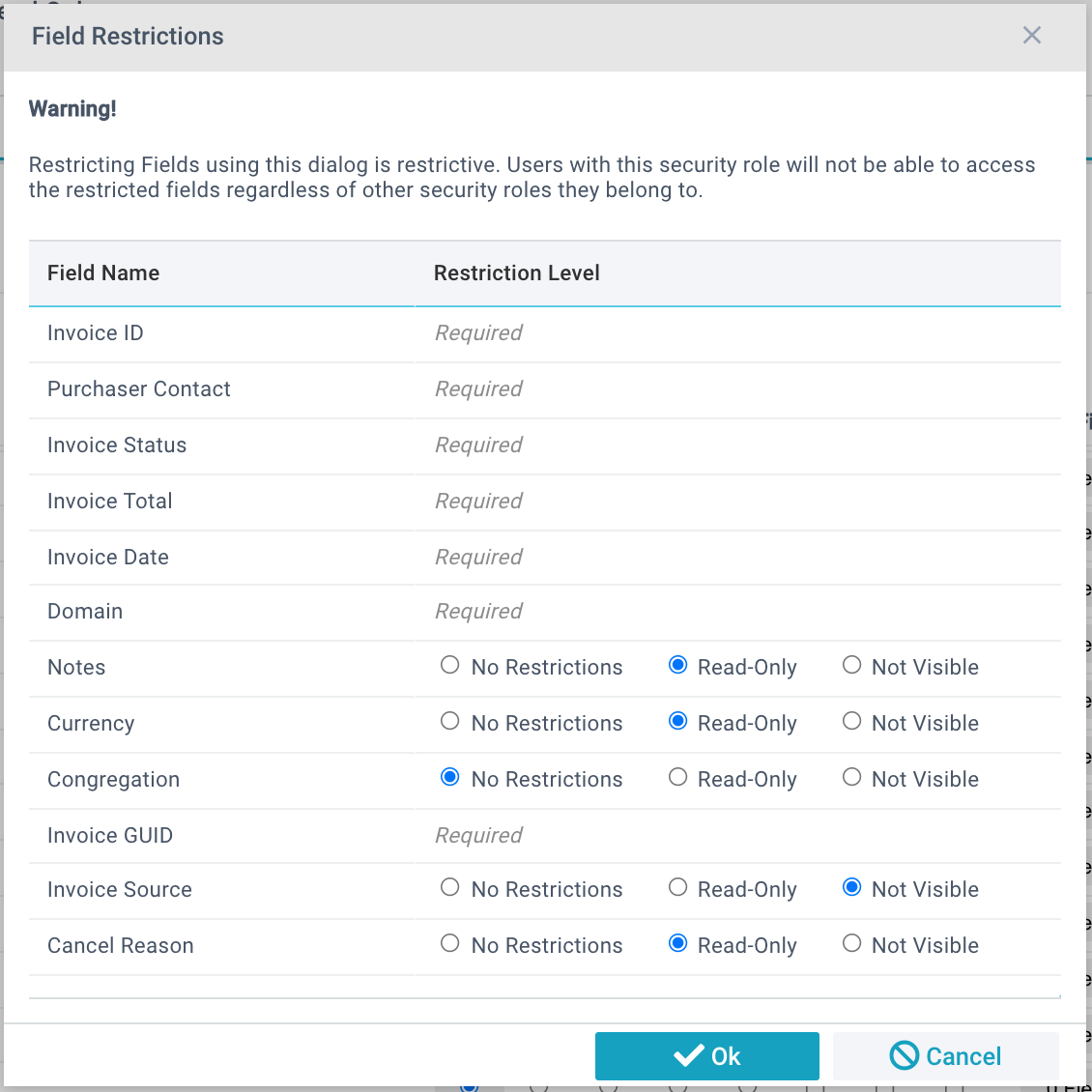
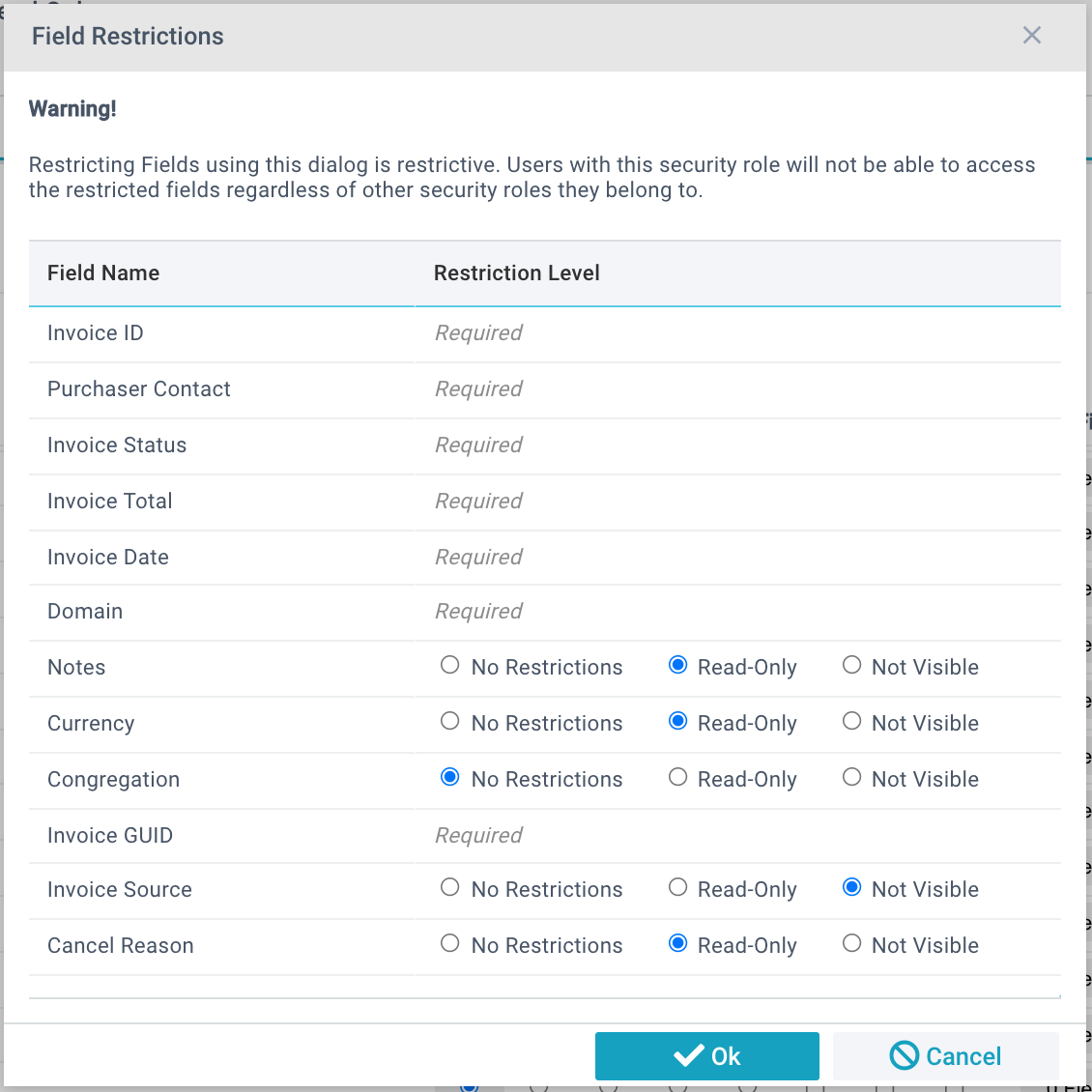
- Field Restrictions are subtractive, not additive. In other words, anyone in a Security Role with Field Restriction will not have permission to that field, regardless of their other Roles. This is different than Page permissions (which are additive) where the sum of all permissions is granted.
- It is possible to expose a field that is otherwise secured if it is made part of a Page View or a Report. Currently, the design for field-level restrictions is based on the table and not the page. Thus please keep in mind the following:
- Make sure the fields you restrict are NOT on the default field list of the page as these will populate in grid layout.
- Make sure fields you restrict are restricted in a Security Role for users who shouldn't see them ever.
- Ensure that the restrictive roles are not applied to people who might need them even on another page (especially in the case of filtered pages).
- Remember that field-level restrictions are based on the table, not a page (so be careful with filtered pages).
- Some fields are labeled in the Field Restrictions window as "Required." These fields cannot be set to Read-Only or Not Visible. For these fields, consider setting the Permissions to the more restrictive setting and edit the data in a different way (the Add/Edit Family Tool, for example, to edit Contact record information). Alternatively, consider creating a Process or an Item Notification to trigger when changes to the field you desire to restrict have been changed.
- Be aware that some fields are set to read-only on a database level and will also not be controllable via field-level restrictions. The fields start with a "_" in their field name.
- To determine which Security Roles have Field Level Restrictions, use a View on the Security Roles page. See View Example: Security Role Field Restrictions for more information.
Best Practices
Restriction Only Roles: The best way to use Field Restrictions is to create a Security Role for each set of Field Restrictions and put anyone who should have those restrictions in the role. It will override their other permissions. Do not grant Page permissions in these roles.
Adopt a Naming Convention: By placing "Restrictions" or some other keyword in your Security Roles used for these restrictions, you can more easily manage them.
Configuring Field-Level Restrictions
- Administration > Security Roles
- Open the desired Security Role
- Click Edit
- Find the page where you want to restrict specific fields and click on the button under the Fields column.
- Configure the specific fields on the pop-up window that opens
- Click Okay to save the restrictions you made in the pop-up window
- Save the Security Role
User Walktrough—Restricting the "Last Donation Date" from specific users
1. Administration > Security Roles
2. Click New
3. Give the role a name, such as Restrict Last Donation Date
4. Scroll down to the Households page
5. Click on the Fields button (under the Fields column)
6. In the Fields List, find Last Donation
7. Set the Not Visible bit field
8. Click OK
9. Assign this role to anyone who you don’t want to have access to this field.
Note: The "Last Donation" field is auto-populated by a nightly service. There is a configuration value called "AddLastDonationDate" that must be set to "YES" in order for this value to be populated.